Generate Private Key From Script
Mar 27, 2019 Switch to the PuTTYgen window, select all of the text in the Public key for pasting into authorizedkeys file box, and copy it to the clipboard (Ctrl+C). Then, switch back to the editor and insert the data into the open file, making sure it ends up all on. Oct 19, 2015 Hi. I am trying to generate a private key using powershell and eventually export it to a pfx file but I have run in to difficulties. When I try to use the export method of the private key com object it fails, I have tried various combinations of arguments without success. In cryptocurrencies, a private key allows a user to gain access to their wallet. The person who holds the private key fully controls the coins in that wallet. For this reason, you should keep it secret. And if you really want to generate the key yourself, it makes sense to generate it in a secure way. Mar 07, 2019 steal bitcoin private key, steal bitcoin free, how hackers steal bitcoins, steal bitcoin from blockchain, steal bitcoin from wallet, steal bitcoin with private key script freebitco.in 2018 script.
Generate Private Key From Script Pdf
How to Generate a Public/Private KeyPair for Use With Solaris Secure Shell
Oct 19, 2015 Hi. I am trying to generate a private key using powershell and eventually export it to a pfx file but I have run in to difficulties. When I try to use the export method of the private key com object it fails, I have tried various combinations of arguments without success.
Users must generate a public/private key pair when their site implementshost-based authentication or user public-key authentication. For additionaloptions, see the ssh-keygen(1) manpage.
Before You Begin
Determine from your system administrator if host-based authenticationis configured.
Generate Private Key From Script Free
Start the key generation program.
where -t is the type of algorithm, one of rsa, dsa, or rsa1.
Specify the path to the file that will hold the key.
Bydefault, the file name id_rsa, which represents an RSAv2 key, appears in parentheses. You can select this file by pressing the Return key. Or, you can type an alternative file name.
The file name of the public key is created automatically by appendingthe string .pub to the name of the private key file.
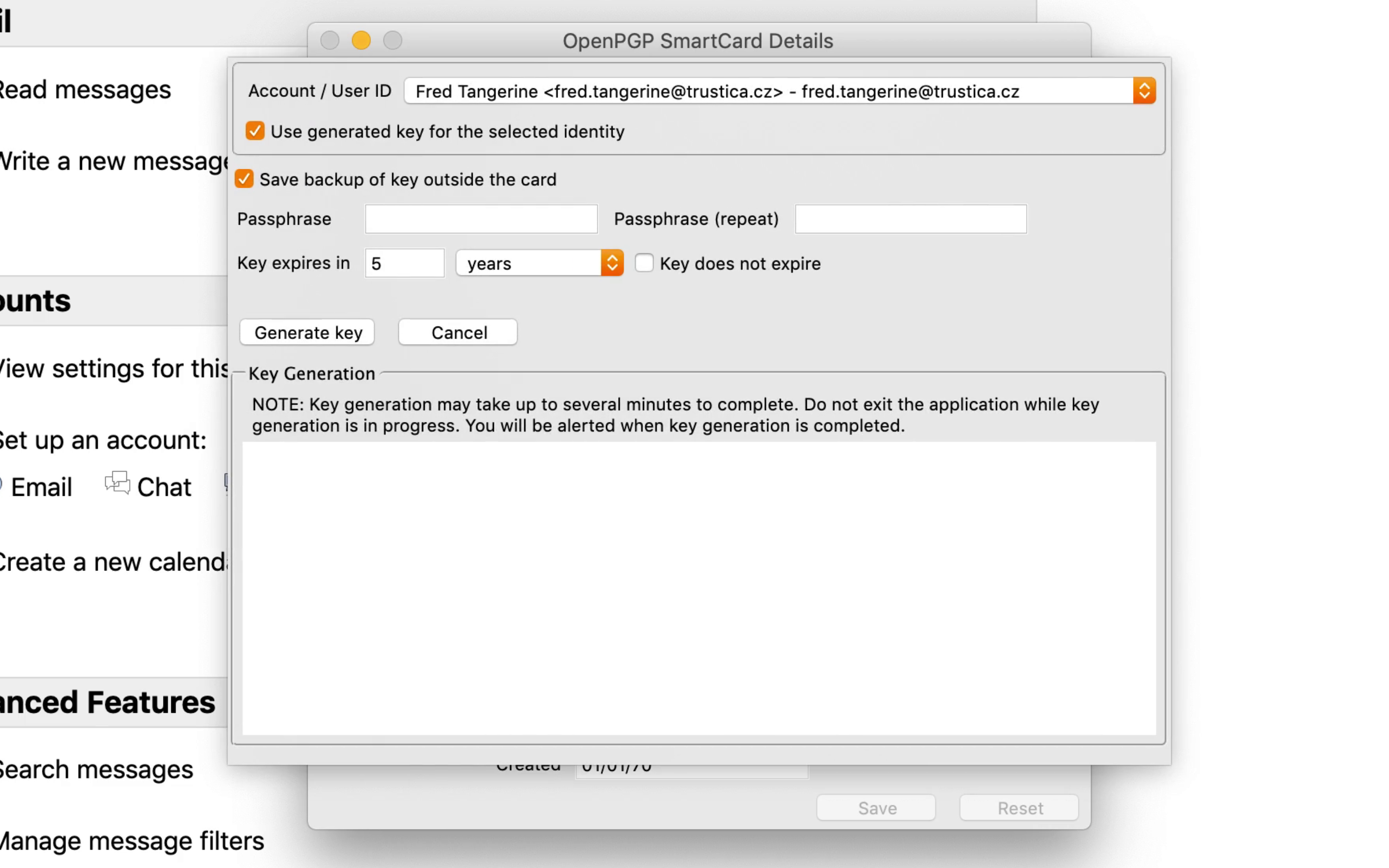
Type a passphrase for using your key.
This passphraseis used for encrypting your private key. A null entry is stronglydiscouraged. Note that the passphrase is not displayed when youtype it in.
Retype the passphrase to confirm it.
Check the results.
Check that the path to the keyfile is correct.
At this point, you have created a public/private key pair.
Choose the appropriate option:
If your administrator has configuredhost-based authentication, you might need to copy the local host's publickey to the remote host.
You can now log in to the remote host.For details, see How to Log In to a Remote Host With Solaris Secure Shell.
Type the command on one line with no backslash.
When you are prompted, supply your login password.
If your site uses user authentication with public keys, populateyour authorized_keys file on the remote host.
Copy your public key to the remote host.
Type thecommand on one line with no backslash.
When you are prompted, supply your login password.
Whenthe file is copied, the message “Key copied” is displayed.
(Optional) Reduce the prompting for passphrases.
For a procedure, see How to Reduce Password Prompts in Solaris Secure Shell. For more information, see the ssh-agent(1) and ssh-add(1) man pages.
Generate Private Key From Script Download
Example 19–2 Establishing a v1 RSA Key for a User
In the following example, the user cancontact hosts that run v1 of the Solaris Secure Shell protocol. To be authenticated by v1hosts, the user creates a v1 key, then copies the public key portion to theremote host.